Add to Compare
Add to Compare
Add to Compare
Compare Rippling IT vs Endpoint Detection And Response
Overall Rating
Ease of Use
9
0
Customer Support
9
0
Value for Money
9
0
Functionality
9
0
Specifications
Anti-Virus And Anti-Malware
Backup And Disaster Recovery
Data Encryption
Intrusion Detection
Multi-Factor Authentication
Security Audits And Reporting
Security Information And Event Management (SIEM)
Vulnerability Management
Pros and Cons
Pros
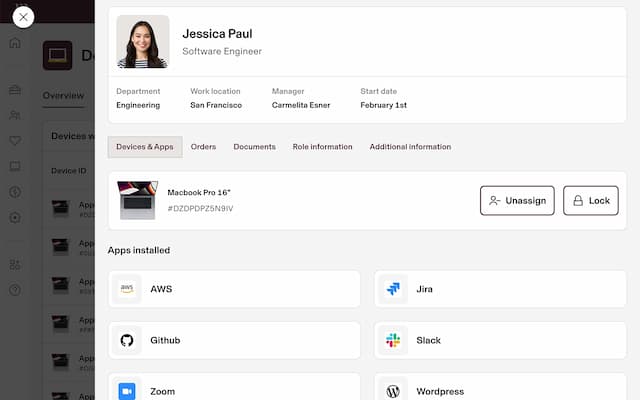
Supports easier control over devices and policies
Enhances security through centralized access controls
Simplifies employee onboarding and offboarding processes
Provides deep, real-time visibility into all endpoint activities, eliminating security blind spots
Enables proactive threat hunting to uncover sophisticated or fileless attacks that traditional tools miss
Offers rapid, remote response capabilities to immediately contain a threat and minimize damage.
Cons
Occasional delays in syncing data across systems
Advanced features may require additional setup time
Extensive capabilities may initially overwhelm users