Add to Compare
Add to Compare
Add to Compare
Compare Risk Ledger vs SearchLight
Overall Rating
Ease of Use
9
0
Customer Support
9
0
Value for Money
10
0
Functionality
9
0
Specifications
Backup And Disaster Recovery
Data Encryption
Intrusion Detection
Multi-Factor Authentication
Security Information And Event Management (SIEM)
Vulnerability Management
Pros and Cons
Pros
Streamlines supplier onboarding and risk assessment processes
Reduces manual effort with centralized risk data
Enhances visibility and transparency across supply chains
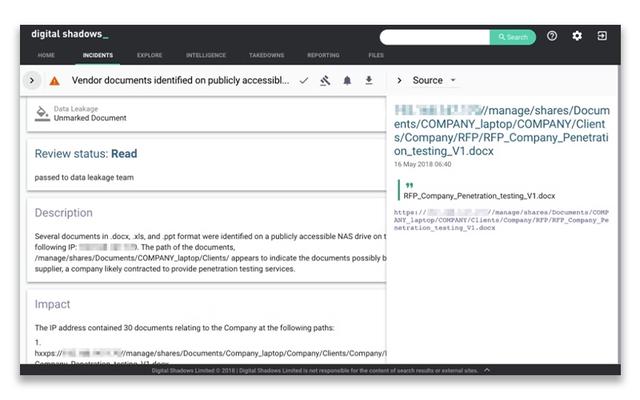
Proactively prevents data exposure and sensitive leaks
Strengthens brand protection against impersonation attacks
Reduces vulnerabilities to minimize potential cyber threats
Cons
Data relies on self-assessed supplier input
Bulk supplier invitation process could be improved
Initial setup can be complex for new users
Documentation gaps may hinder user workflows