Add to Compare
Add to Compare
Add to Compare
Compare ThreatLocker vs Corsha
Overall Rating
Ease of Use
9
0
Customer Support
10
0
Value for Money
10
0
Functionality
10
0
Specifications
Anti-Virus and Anti-Malware
Cloud Security
Data Encryption
Firewall Protection
Intrusion Detection
Multi-Factor Authentication
Phishing Prevention
Security Audits and Reporting
Security Information And Event Management (SIEM)
Security Measure
Threat Intelligence
Vulnerability Management
Web Application Security
Web Filtering
Pros and Cons
Pros
Mobile app
Extensive customization options
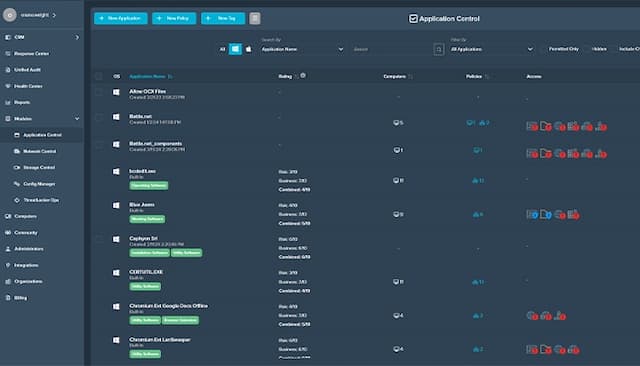
User-friendly management interface available
Excellent customer support
Provides visibility on client connections
Purpose-built for OT environments
Automates machine identity management
Cons
Limited third-party integrations available
Initial workload of onboarding software
Advanced features may overwhelm users
Primarily for enterprise-scale deployments
Potential for complex initial setup